Jailbreaking (AI)
Explore how AI jailbreaking bypasses safety guardrails and learn how to mitigate risks. Protect Ultralytics YOLO26 models with robust defense and monitoring.
Jailbreaking in the context of
artificial intelligence refers to the
practice of bypassing the ethical guardrails, safety filters, and operational constraints programmed into an AI model.
Originally a term used for bypassing hardware restrictions on devices like smartphones, AI jailbreaking involves
crafting specific, often manipulative inputs that trick the model into generating restricted content, executing
unauthorized commands, or revealing sensitive system prompts. As AI becomes increasingly integrated into critical
infrastructure, understanding these vulnerabilities is essential for developing robust
AI safety measures and preventing misuse.
Differentiating Jailbreaking From Related Concepts
While jailbreaking shares similarities with other security vulnerabilities in machine learning, it is important to
distinguish it from related terms:
-
Prompt Injection: This involves inserting
malicious instructions into a legitimate user prompt to hijack a model's intended output. Jailbreaking is a broader
category that specifically aims to entirely override the model's core safety protocols.
-
AI Red Teaming: This is an authorized, proactive
testing methodology where security professionals intentionally attempt to jailbreak a system to identify and patch
vulnerabilities before deployment.
-
Adversarial Attacks: Often used in
computer vision, these involve subtly altering
input data (like adding invisible noise to an image) to force a model into making a misclassification, whereas
jailbreaking typically focuses on linguistic or logical manipulation.
Real-World Examples of AI Jailbreaking
Jailbreaking manifests differently depending on the modality of the AI system, impacting both text-based and
vision-based architectures:
-
Exploiting Large Language Models: Attackers often use complex role-playing scenarios or
hypothetical frameworks to force
large language models to ignore their
safety training. For example, a user might prompt an AI to act as a "fictional author writing a story about a
hacker," successfully
tricking the model into outputting malicious code or
instructions for dangerous activities that its filters would normally block. Recent research by Anthropic has also
highlighted advanced methods like
many-shot jailbreaking techniques, which
overload the model's context window to bypass restrictions.
-
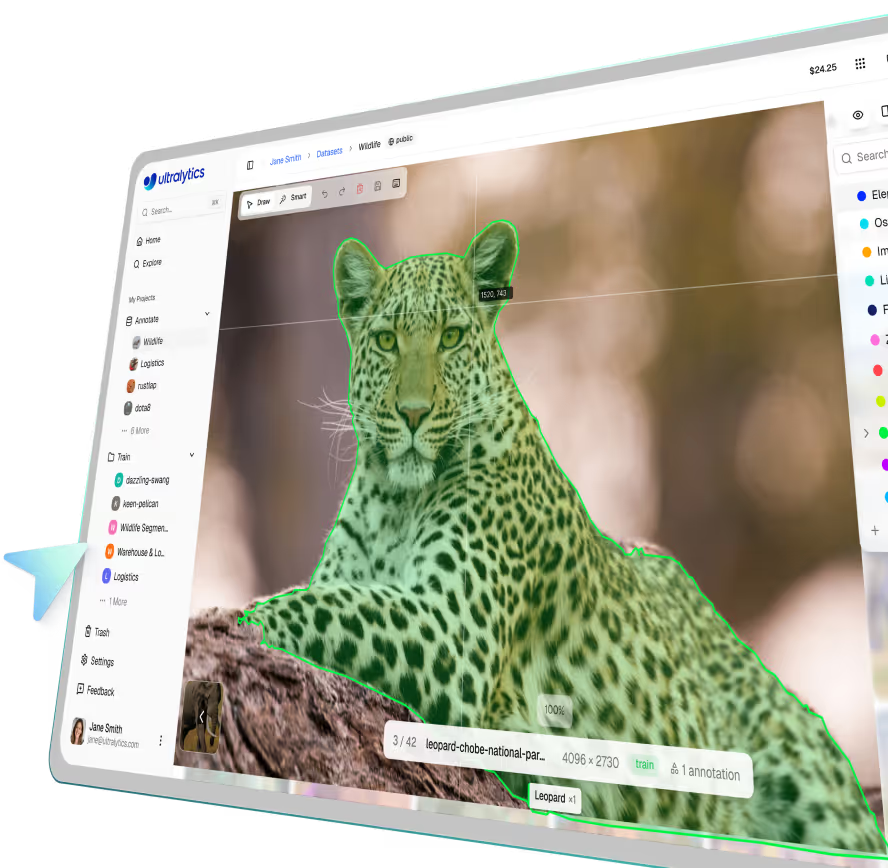
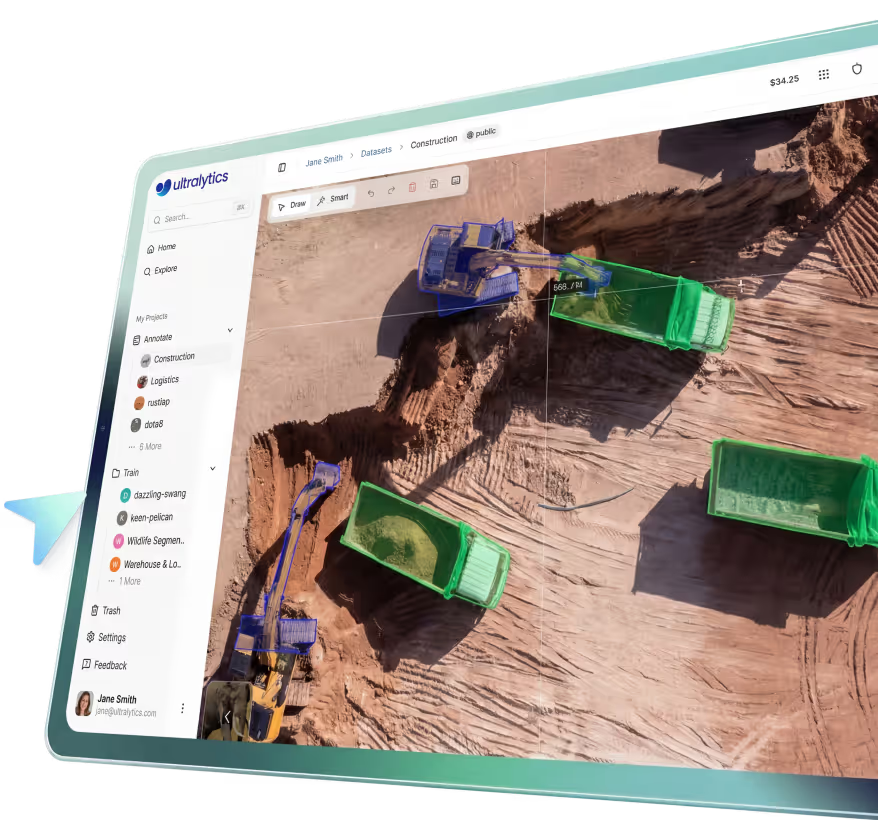
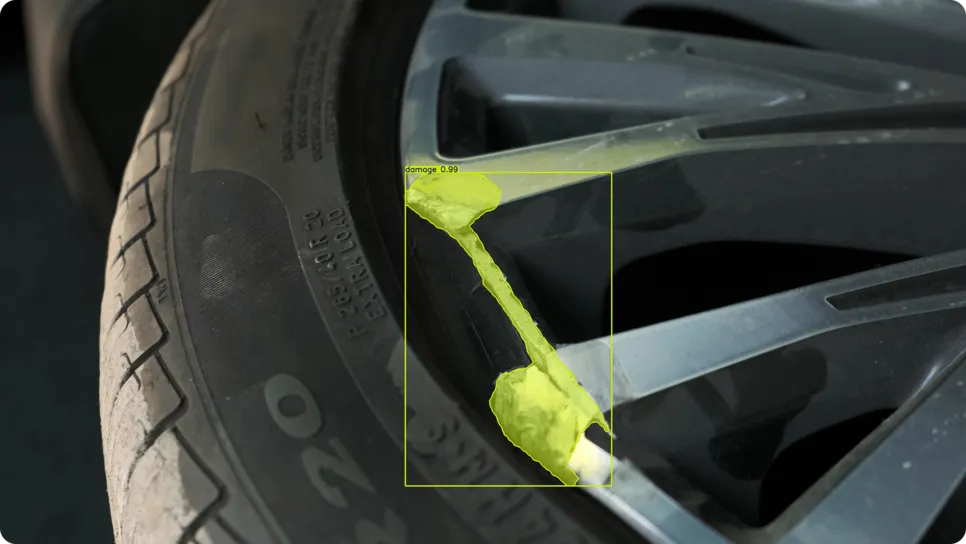
Multimodal and Vision System Attacks: As models evolve to process both text and images,
recent research on multimodal jailbreaks demonstrates that attackers
can embed malicious text instructions within an image. When a vision-language model processes the image, the hidden
text triggers a jailbreak. In physical security systems, adversarial inputs—such as a specifically patterned patch
on clothing—can act as a visual jailbreak, rendering the person invisible to automated surveillance models.
Mitigating Jailbreak Risks in AI Models
Securing models against these exploits requires a multi-layered defense strategy. Developers follow
OpenAI safety guidelines and frameworks like the
NIST AI Risk Management Framework to establish baseline
security.
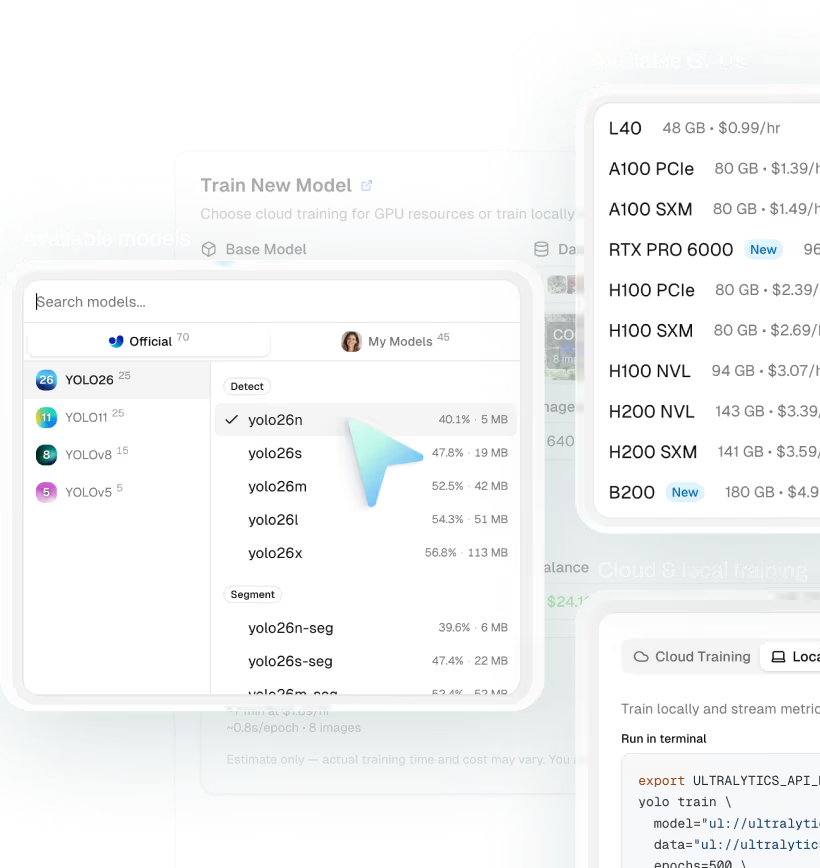
To prevent visual adversarial attacks, engineers rely on comprehensive
data augmentation during training. By
intentionally introducing noise, blurring, and varying lighting conditions, the model learns to maintain high accuracy
even when faced with manipulated inputs. Furthermore, continuously
monitoring deployed models using tools
available on the Ultralytics Platform helps identify unusual inference
patterns that might indicate an ongoing attack, ensuring strong
data security for enterprise deployments.
Testing Model Robustness
To ensure your computer vision models are resilient against subtle input manipulations, you can simulate basic
adversarial machine learning scenarios using
Python. This helps verify that a model like
Ultralytics YOLO26 continues to perform reliably
when exposed to noisy or slightly altered data.
import cv2
from ultralytics import YOLO
# Load an Ultralytics YOLO26 model for robust inference testing
model = YOLO("yolo26n.pt")
# Load a test image and apply simulated adversarial noise
img = cv2.imread("security_feed.jpg")
noisy_img = cv2.add(img, 15) # Inject slight pixel noise to test robustness
# Run prediction to verify the model still detects objects accurately
results = model(noisy_img)
results[0].show()
By actively testing for vulnerabilities and incorporating robust safety measures, developers can successfully learn
how AI jailbreaks can be mitigated, fostering trust and reliability in modern AI systems. For a deeper understanding of model behavior and
interpretability, explore the principles of
explainable AI.